4 Top Security Automation Use Cases
- Rajaguru T

With Gartner recently declaring that SOAR (security orchestration, automation, and response) is being phased out in favor of generative AI-based solutions, this article will explore in detail four key security automation use cases.
1. Enriching Indicators of Compromise (IoCs)
Indicators of compromise (IoCs), such as suspicious IP addresses, domains, and file hashes, are vital in identifying and responding to security incidents.
Manually gathering information about these IoCs from various sources can be labor-intensive and slow down the response process.
Automating the enrichment of IoCs can greatly enhance the efficiency of your security operations.
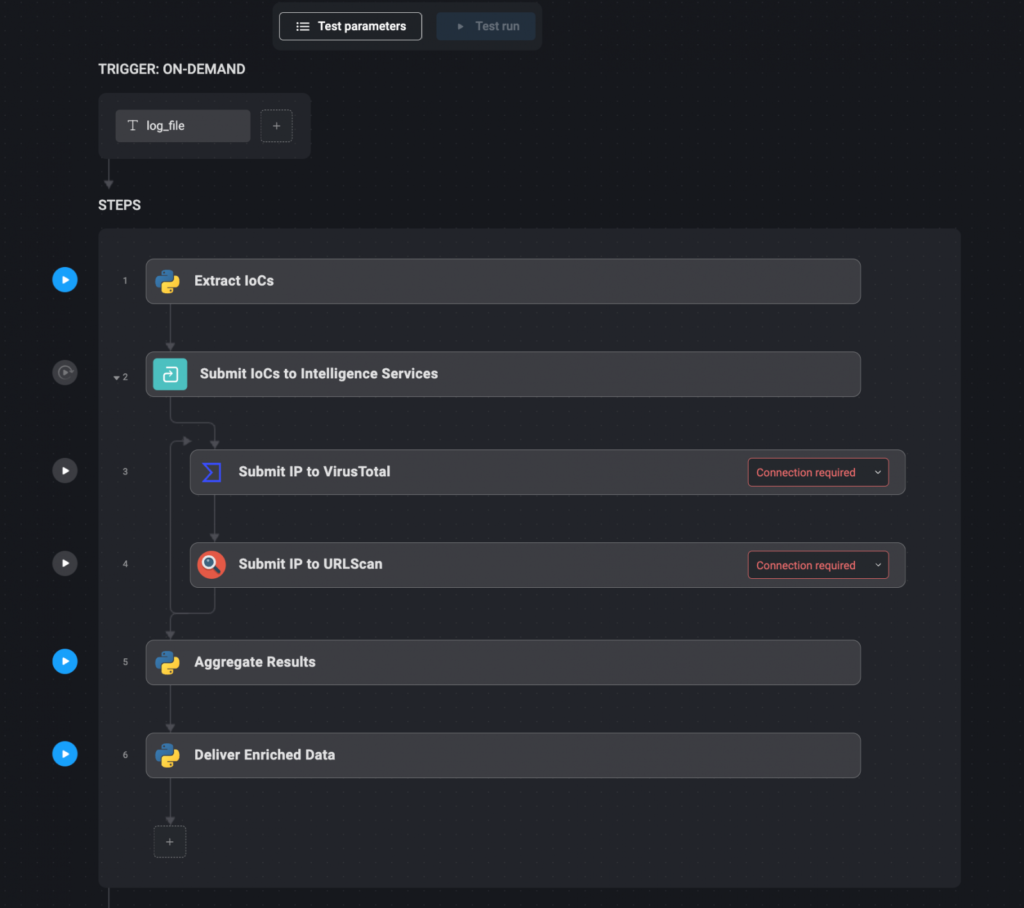
Automation workflow:
- Extract IoCs: Automatically extract relevant IoCs from security logs or alerts using text parsing tools or other automated methods.
- Submit IoCs to Intelligence Services: Once extracted, the IoCs are automatically submitted to various threat intelligence services, such as VirusTotal, URLScan, and AlienVault, via their APIs. These services can provide additional context, such as whether the IP address has been associated with known threats or if the domain has been flagged for suspicious activity.
- Aggregate Results: The results from these intelligence services are aggregated into a single, comprehensive report. This step ensures that all relevant information is available in one place, making it easier for security analysts to assess the threat.
- Deliver Enriched Data: The enriched IoC data is then delivered through communication channels like Slack, or directly added to the relevant incident ticket within the security management system. This ensures that all necessary information is immediately accessible to those who need it.
2. Monitoring Your External Attack Surface
The external attack surface of an organization includes all the external-facing assets that could potentially be exploited by attackers.
These assets include domains, IP addresses, subdomains, exposed services, and more.
Regular monitoring of these assets is important for identifying and mitigating potential vulnerabilities before they are exploited.
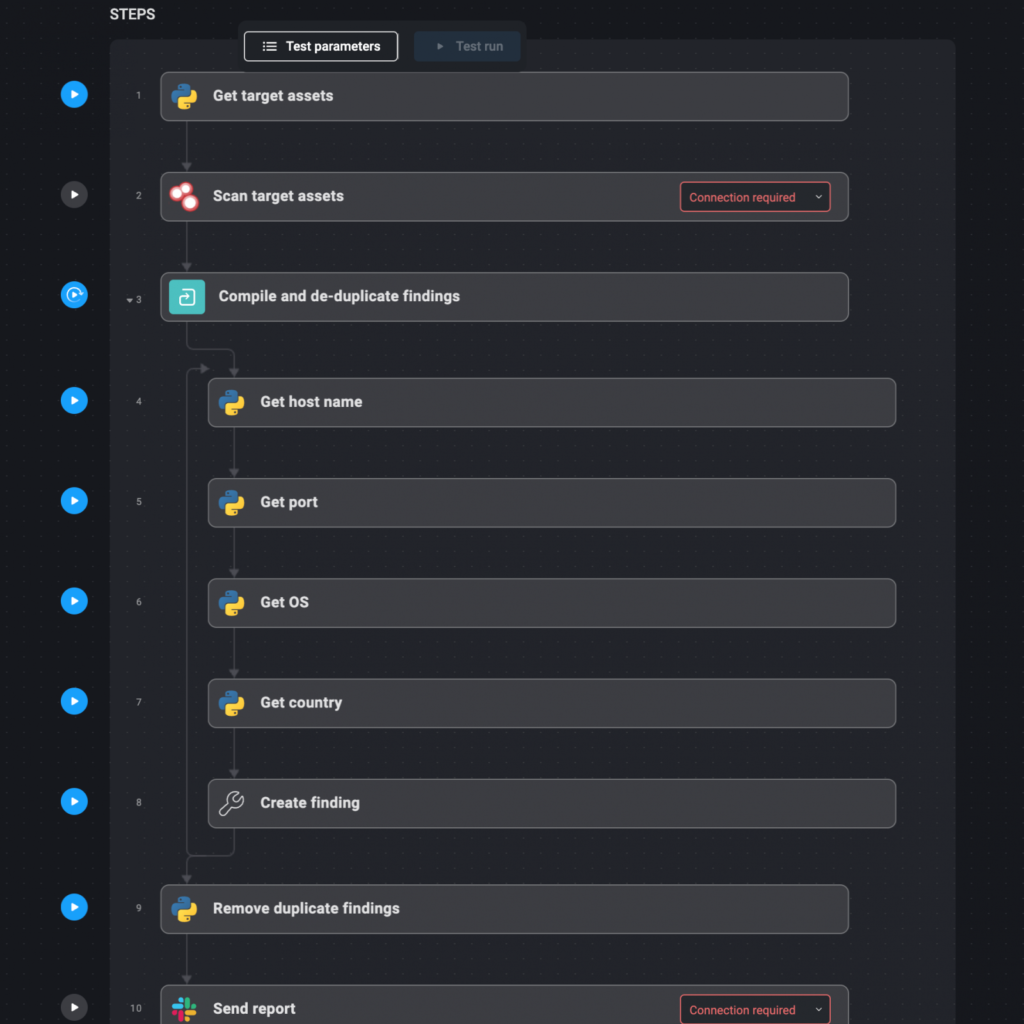
Automation workflow:
- Define Target Assets: Start by defining the domains and IP addresses that make up your external attack surface. These should be documented in a file that the automation system can reference.
- Automated Reconnaissance: Use tools like Shodan to scan these assets on a weekly or monthly basis. Shodan can help identify open ports, exposed services, and other vulnerabilities.
- Compile and De-duplicate Findings: The results from these scans are automatically compiled into a report. Any duplicate findings are removed to ensure that the report is concise and actionable.
- Deliver Weekly Reports: The final report is delivered via email, Slack, or another preferred communication channel. This report highlights new or changed assets, potential vulnerabilities, and any redundant applications that may pose a risk.
3. Scanning for Web Application Vulnerabilities
Web applications are frequent targets for attackers, making regular vulnerability scans useful for maintaining security.
Tools like OWASP ZAP and Burp Suite automate the process of identifying common vulnerabilities, including outdated software and misconfiguration.
These scans also detect input validation vulnerabilities, helping to secure web applications.
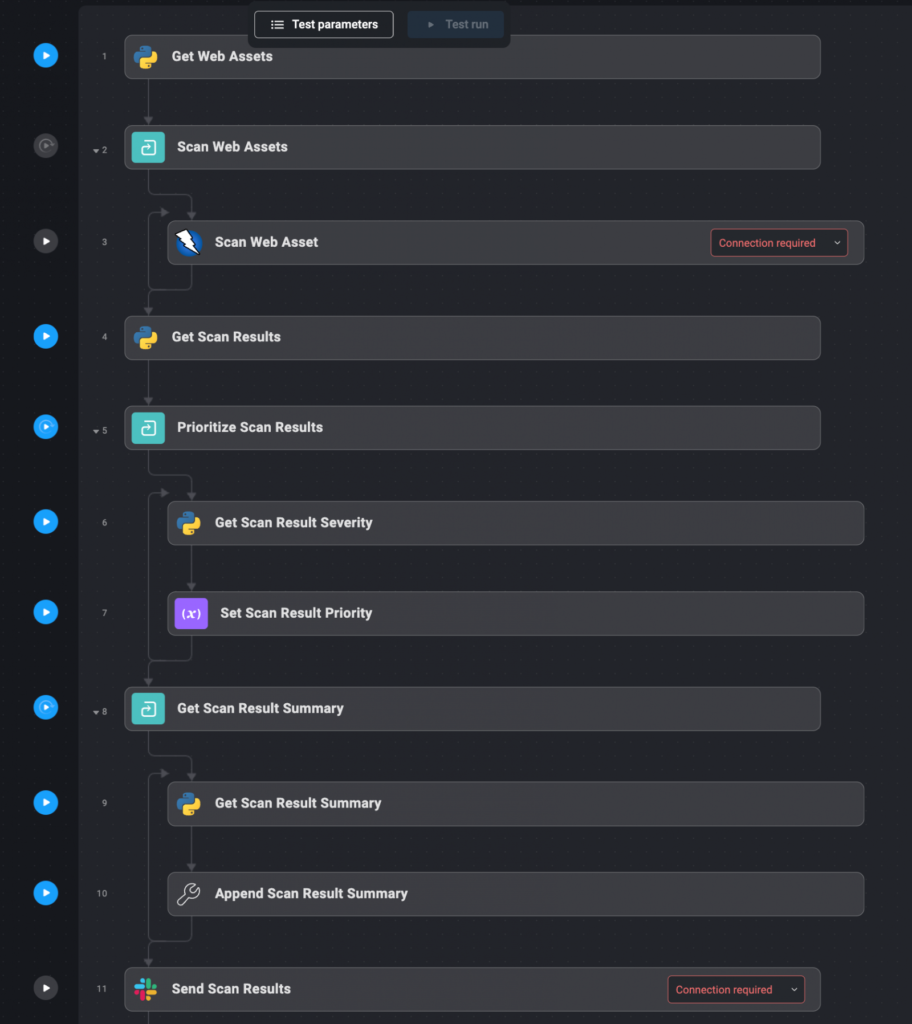
Automation workflow:
- Define Web Assets: Begin by listing all the domains and IP addresses that host your organization’s web applications. These assets should be documented in a file for easy reference by the automation system.
- Automated Vulnerability Scanning: The defined web assets are automatically sent to scanning tools like OWASP ZAP and Burp Suite. These tools perform comprehensive scans to identify vulnerabilities, including those that are commonly exploited by attackers.
- Collect and Prioritize Results: The results from the scans are automatically collected and prioritized based on the severity of the vulnerabilities detected. Critical/severe vulnerabilities are highlighted for immediate action.
- Deliver Results: The prioritized results are delivered to the relevant teams via Slack or as an enriched ticket within the incident management system. This ensures that the right people are notified of the vulnerabilities and can take appropriate action.
4. Monitoring Email Addresses For Stolen Credentials
Monitoring for compromised credentials is an important aspect of an organization’s cybersecurity strategy.
Have I Been Pwned (HIBP) is a widely used service that aggregates data from various breaches to help individuals and organizations determine if their credentials have been compromised
Automating the process of checking HIBP for exposed credentials can help organizations quickly identify and respond to potential security incidents.
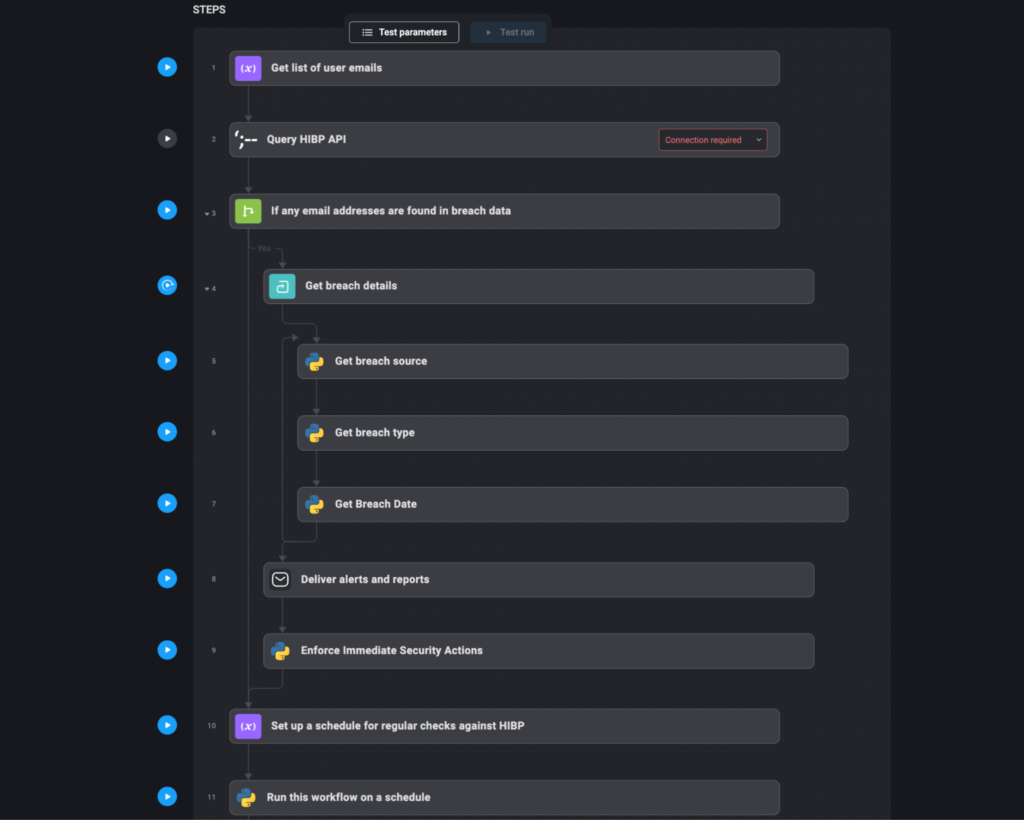
Automation workflow:
- Compile User Emails and Domains: Create a list of user email addresses or domains that need to be monitored. This list should include all relevant user accounts within the organization, especially those with privileged access.
- Query HIBP API: Automatically query the HIBP API with the compiled list of email addresses or domains. This step involves sending requests to HIBP to check if any of the email addresses have appeared in known data breaches.
- Aggregate and Analyze Results: Collect the responses from HIBP. If any email addresses or domains are found in breach data, the details of these breaches (such as the breach source, type of exposed data, and date of the breach) are aggregated and analyzed.
- Deliver Alerts and Reports: If compromised credentials are detected, automatically generate an alert. This alert can be sent via email, Slack, or integrated into the organization’s incident response system as a high-priority ticket. Include detailed information about the breach, such as the affected email addresses, the nature of the exposure, and recommended actions (e.g., forcing password resets).
- Enforce Immediate Security Actions: Based on the severity of the breach, the system can automatically enforce security actions. For example, it might trigger a password reset for affected accounts, notify the users involved, and increase monitoring on accounts that were compromised.
- Regular Scheduled Checks: Set up a schedule for regular checks against HIBP, such as weekly or monthly queries. This ensures that the organization remains aware of any new breaches that might involve their credentials and can respond promptly.
Frequently Asked Questions
Below we will answer some frequently asked questions about the automated workflows above and how they can help in a practical way.
- Don’t third-party services offer automation workflows anyway?
Many services provide APIs that allow for automating parts of the workflow, like fetching data. However, building an end-to-end automated workflow typically requires coding and configurations. Replicating the entire workflow with scripts offers flexibility but is less powerful, as changes could break it. Leveraging available APIs with a centralized automation platform provides a stable, scalable solution. - Can’t we just replicate this whole thing with bash scripts?
Yes, it is possible to write Bash/PowerShell scripts to automate the security tasks mentioned in the article. Scripts offer flexibility that is lacking in manual processes. However, scripts require ongoing maintenance, and any changes could break the workflow. They may also lack advanced features like central management, scheduling, alerting, and reporting, which are offered by dedicated automation platforms like Blink Ops. A proper platform is more reliable and efficient for complex, long-running automation requirements. - How does automating IoC enrichment help?
Automating IoC enrichment speeds up the response process by gathering threat intelligence on indicators like IPs, domains, and file hashes from multiple sources simultaneously via APIs. This provides security teams with a single comprehensive report with the necessary context to assess threats quickly, rather than spending time manually searching different sources. It improves efficiency and situational awareness, enabling informed decisions to be made quickly.
Ref: https://www.bleepingcomputer.com/news/security/4-top-security-automation-use-cases-a-detailed-guide/
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
This was beautiful Admin. Thank you for your reflections.
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
I’m often to blogging and i really appreciate your content. The article has actually peaks my interest. I’m going to bookmark your web site and maintain checking for brand spanking new information.
very informative articles or reviews at this time.
Nice post. I learn something totally new and challenging on websites
Awesome! Its genuinely remarkable post, I have got much clear idea regarding from this post
There is definately a lot to find out about this subject. I like all the points you made
Lois Sasson Hi there to all, for the reason that I am genuinely keen of reading this website’s post to be updated on a regular basis. It carries pleasant stuff.
“Your writing style is engaging and clear, love it!”
“Great content, learned a lot from this post!”
“Amazing post, keep up the good work!”
Its like you read my mind You appear to know so much about this like you wrote the book in it or something I think that you can do with a few pics to drive the message home a little bit but other than that this is fantastic blog A great read Ill certainly be back
I have been browsing online more than three hours today yet I never found any interesting article like yours It is pretty worth enough for me In my view if all website owners and bloggers made good content as you did the internet will be a lot more useful than ever before
“Thanks for sharing such valuable information!”
“Amazing post, keep up the good work!”
“Thanks for sharing such valuable information!”
“This post has helped me solve my issue, thanks a ton!”
“I appreciate the detailed explanation, very helpful!”
“I appreciate the detailed explanation, very helpful!”
“I appreciate the detailed explanation, very helpful!”
mly informative and well-written!”
Usually I do not read article on blogs however I would like to say that this writeup very compelled me to take a look at and do so Your writing taste has been amazed me Thanks quite nice post
“This post has helped me solve my issue, thanks a ton!”
Masterful analysis! Your understanding of creative expression perfectly aligns with what Sprunki Game brings to the table. The way Sprunki Game empowers users through its innovative interface and diverse sound library showcases the future of interactive music creation. It’s a game that inspires innovation!
Thank you for always being open and honest with your readers It’s refreshing to see a blogger who is unafraid to be vulnerable and real
Normally I do not read article on blogs however I would like to say that this writeup very forced me to try and do so Your writing style has been amazed me Thanks quite great post
Your blog is a beacon of light in the often murky waters of online content. Your thoughtful analysis and insightful commentary never fail to leave a lasting impression. Keep up the amazing work!
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing at at this place.
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing at at this place.
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
Your writing is like a breath of fresh air in the often stale world of online content. Your unique perspective and engaging style set you apart from the crowd. Thank you for sharing your talents with us.
hiI like your writing so much share we be in contact more approximately your article on AOL I need a specialist in this area to resolve my problem Maybe that is you Looking ahead to see you
This is my first time pay a quick visit at here and i am really happy to read everthing at one place
Good post! We will be linking to this particularly great post on our site. Keep up the great writing
One of the most useful launches I’ve seen!
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
This is my first time pay a quick visit at here and i am really happy to read everthing at one place
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing at at this place.
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
I appreciate you sharing this blog post. Thanks Again. Cool.
You’re so awesome! I don’t believe I have read a single thing like that before. So great to find someone with some original thoughts on this topic. Really.. thank you for starting this up. This website is something that is needed on the internet, someone with a little originality!
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
This was beautiful Admin. Thank you for your reflections.
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents.
Very well presented. Every quote was awesome and thanks for sharing the content. Keep sharing and keep motivating others.
Good post! We will be linking to this particularly great post on our site. Keep up the great writing
I like the efforts you have put in this, regards for all the great content.
very informative articles or reviews at this time.
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents.
I do not even understand how I ended up here, but I assumed this publish used to be great
I truly appreciate your technique of writing a blog. I added it to my bookmark site list and will
Hi there to all, for the reason that I am genuinely keen of reading this website’s post to be updated on a regular basis. It carries pleasant stuff.
I truly appreciate your technique of writing a blog. I added it to my bookmark site list and will
Pretty! This has been a really wonderful post. Many thanks for providing these details.
Awesome! Its genuinely remarkable post, I have got much clear idea regarding from this post
This was beautiful Admin. Thank you for your reflections.
I appreciate you sharing this blog post. Thanks Again. Cool.
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents.
There is definately a lot to find out about this subject. I like all the points you made
I very delighted to find this internet site on bing, just what I was searching for as well saved to fav
I truly appreciate your technique of writing a blog. I added it to my bookmark site list and will
This is my first time pay a quick visit at here and i am really happy to read everthing at one place
very informative articles or reviews at this time.
There is definately a lot to find out about this subject. I like all the points you made
Awesome! Its genuinely remarkable post, I have got much clear idea regarding from this post
You’re so awesome! I don’t believe I have read a single thing like that before. So great to find someone with some original thoughts on this topic. Really.. thank you for starting this up. This website is something that is needed on the internet, someone with a little originality!
naturally like your web site however you need to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again.
I truly appreciate your technique of writing a blog. I added it to my bookmark site list and will
This was beautiful Admin. Thank you for your reflections.
I just like the helpful information you provide in your articles
I’m often to blogging and i really appreciate your content. The article has actually peaks my interest. I’m going to bookmark your web site and maintain checking for brand spanking new information.
I just like the helpful information you provide in your articles
I just like the helpful information you provide in your articles
Awesome! Its genuinely remarkable post, I have got much clear idea regarding from this post
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing at at this place.
Good post! We will be linking to this particularly great post on our site. Keep up the great writing
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
I just like the helpful information you provide in your articles
You’re so awesome! I don’t believe I have read a single thing like that before. So great to find someone with some original thoughts on this topic. Really.. thank you for starting this up. This website is something that is needed on the internet, someone with a little originality!
naturally like your web site however you need to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again.
I very delighted to find this internet site on bing, just what I was searching for as well saved to fav
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
Pretty! This has been a really wonderful post. Many thanks for providing these details.
Hi there to all, for the reason that I am genuinely keen of reading this website’s post to be updated on a regular basis. It carries pleasant stuff.
Awesome! Its genuinely remarkable post, I have got much clear idea regarding from this post
This is really interesting, You’re a very skilled blogger. I’ve joined your feed and look forward to seeking more of your magnificent post. Also, I’ve shared your site in my social networks!
Great information shared.. really enjoyed reading this post thank you author for sharing this post .. appreciated
naturally like your web site however you need to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again.
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing at at this place.
Pretty! This has been a really wonderful post. Many thanks for providing these details.
naturally like your web site however you need to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again.
very informative articles or reviews at this time.
I do not even understand how I ended up here, but I assumed this publish used to be great
I really like reading through a post that can make men and women think. Also, thank you for allowing me to comment!
I truly appreciate your technique of writing a blog. I added it to my bookmark site list and will
Pretty! This has been a really wonderful post. Many thanks for providing these details.
naturally like your web site however you need to take a look at the spelling on several of your posts. A number of them are rife with spelling problems and I find it very bothersome to tell the truth on the other hand I will surely come again again.
Nice post. I learn something totally new and challenging on websites
Awesome! Its genuinely remarkable post, I have got much clear idea regarding from this post
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents.
This is really interesting, You’re a very skilled blogger. I’ve joined your feed and look forward to seeking more of your magnificent post. Also, I’ve shared your site in my social networks!
You’re so awesome! I don’t believe I have read a single thing like that before. So great to find someone with some original thoughts on this topic. Really.. thank you for starting this up. This website is something that is needed on the internet, someone with a little originality!
Great information shared.. really enjoyed reading this post thank you author for sharing this post .. appreciated
Good post! We will be linking to this particularly great post on our site. Keep up the great writing
I am truly thankful to the owner of this web site who has shared this fantastic piece of writing at at this place.
For the reason that the admin of this site is working, no uncertainty very quickly it will be renowned, due to its quality contents.
Great information shared.. really enjoyed reading this post thank you author for sharing this post .. appreciated
Awesome! Its genuinely remarkable post, I have got much clear idea regarding from this post
This was beautiful Admin. Thank you for your reflections.